HP just did something at Imagine 2026 that might make a lot of IT folks a little uneasy. The company introduced HP TPM Guard, and the pitch is pretty blunt. It’s meant to stop a type of physical attack that can bypass BitLocker. Yes, that BitLocker. The one many businesses trust to keep data safe if a laptop goes missing.
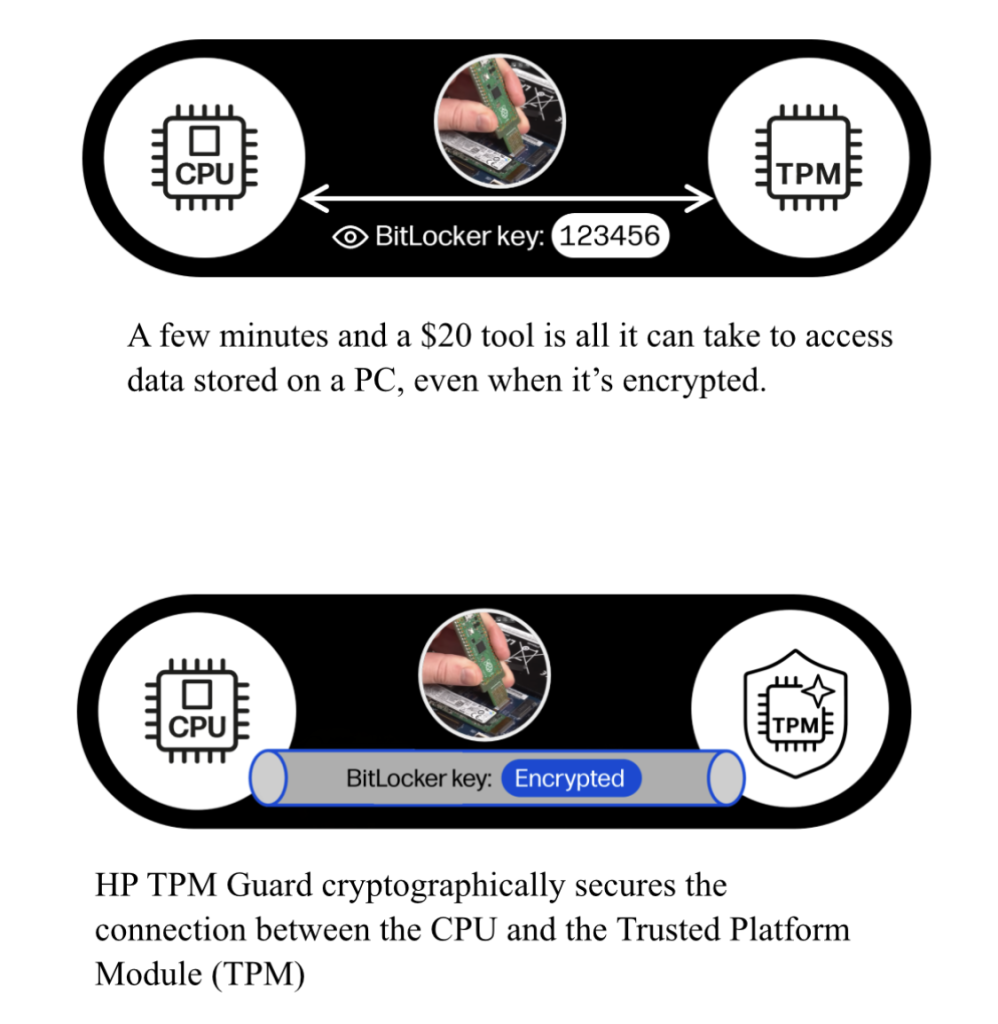
Here’s the problem HP is highlighting. In certain situations, someone with physical access to a machine can tap into the communication between the TPM and the CPU. That opens the door to pulling data off an encrypted drive. According to HP, this can be done quickly, cheaply, and without much skill. That’s not exactly comforting.
TPM Guard is HP’s answer. It creates an encrypted link between the TPM and the processor, and it ties the TPM directly to the system. If someone tries to mess with it or remove it, it stops working. In theory, that shuts down this whole class of attack.
What stands out here is that HP says this happens behind the scenes. No extra setup, no changes for IT, nothing new for users to learn. It just works. Assuming that’s true, that’s the kind of security improvement people actually benefit from, because nobody has to think about it.
Still, this raises a bigger question. If this kind of attack has been possible, how many companies are relying on BitLocker today thinking they’re fully protected? And why hasn’t this been addressed at the hardware level sooner across the industry?
HP says TPM Guard will start rolling out in July 2026 on select G2 commercial PCs. It will come first as a firmware update for supported systems, and later it will ship built in. There’s no added cost, which is nice to hear for once.
Outside of TPM Guard, HP also talked up updates to its Wolf Security lineup. The focus seems to be on tying things together better, reducing overhead, and giving IT more centralized visibility. There’s also a new Wolf Connect cellular option that aims to improve tracking while using less power. Useful, but not exactly headline material.
Then there are the printers. HP is pushing quantum resistant security into new LaserJet Pro 4000 and Enterprise 5000 and 6000 series models. The idea is to prepare for a future where quantum computers can break today’s encryption. That future may or may not arrive anytime soon, but HP clearly thinks customers in regulated industries will care.
One feature that could get some real use is automated redaction on enterprise printers. It can detect and remove sensitive info before documents are shared. If it works well, that could save people from some very avoidable mistakes.
Zooming out, this whole announcement feels less about flashy features and more about locking things down. And honestly, that’s probably where the focus should be right now. As more AI workloads move onto local machines, those devices are holding even more sensitive data than before.
Of course, it’s easy to make security claims on stage. The real story will come once researchers and attackers start poking at this in the wild. For now, though, TPM Guard is a reminder that encryption alone isn’t always enough, especially if someone can get their hands on your hardware.

